On October 29, the Cyberspace Administration of China (CAC) issued a draft (link in Chinese) of Measures on Security Assessment of Data Exports (数据出境安全评估办法) (unofficial English translation here). The draft is now open for public comments until November 28, 2021. The draft is formulated in accordance with China’s Data Security Law, Cybersecurity Law, and Personal Information Protection Law (PIPL). The draft sets out rules for data processors to export certain data abroad. This piece summarizes the main provisions in the draft and compares it with an earlier version of similar measures in 2017.
The draft outlines five types of data that, when being transferred overseas, will undergo two steps of security assessments: self-assessment and administrative assessment. The covered data includes :
- Personal information and important data collected and generated by operators of critical information infrastructure;
- "Exported data containing important data”;
- Personal information processors who have processed personal information of one million people or more;
- Exporting personal information of more than 100,000 people cumulatively or sensitive personal information of more than 10,000 people;
- Other situations required by the cybersecurity agencies for security assessment.
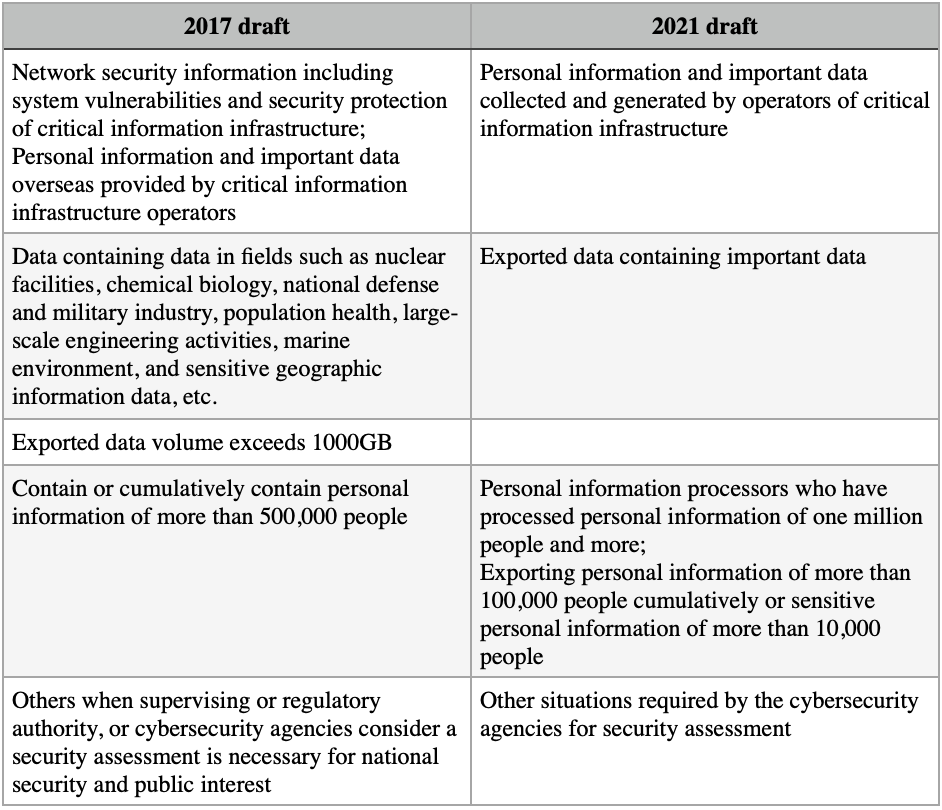
(See table at the end of this piece for a comparison of covered data in this draft with that of a 2017 draft.)
The PIPL defines personal data as various information stored by electronic or other means that are related to identified or identifiable natural persons, which does not include anonymized personal information. It also clarifies that sensitive personal data includes data of minors, as well as biometrics, ethnicities, religious beliefs, specific identities, medical health, financial accounts, whereabouts and others.
As far as important data generated by operators of critical information infrastructure, the Ministry of Industry and Information Technology recently proposed a definition in a draft measure for industry and information sectors. In the proposal, important data would be defined as data which, once at risk, would pose a threat to China's political system, territory, military, economy, culture, society, technology, network, ecology, resources and nuclear security, as well as data related to national security in areas such as overseas interests, biology, space, polar regions, deep sea, artificial intelligence, etc. Important data could also be data with an impact on the development and operation of industry and telecommunication, or data for which leakage would have obvious cascading effects on society and multiple sectors. If the cost of restoring data or mitigating the negative effect of a data breach is very high, such data would be considered important too. The proposal has not been finalized.
If the data falls into the categories mentioned above, data exporters are required to conduct a self-assessment, under which they shall assess the following factors:
- The legitimacy and necessity of purpose, scope, and method of data exports;
- The quantity, scope, type and sensitivity of data and possible risks of exporting such data to national security, public interest, individual rights and organizations;
- The measures and capability of data processors to prevent data leakage and destruction;
- Responsibilities of data recipients and their measures and capabilities of enforcing such responsibilities;
- The risks of data leakage, destruction, alteration and abuse after data exports and re-exports, and ways for individuals to protect personal information;
- Whether the contracts related to data exports sufficiently stipulate data protection duties.
The self-assessment report shall be submitted for an administrative assessment, along with contracts with overseas data recipients and other documents.
The contracts shall include:
- The purpose, method and scope of data exports, as well as the purpose and method of data processing by overseas recipients;
- The location and duration of overseas data storage, and the processing measures for data after the storage period ends, the agreed purpose is fulfilled, or the contract is terminated;
- Binding clauses restricting the transfer of exported data by overseas recipients to other organizations and individuals;
- The safety measures that the overseas recipients should take when the actual control rights or business scope changes substantially, or the legal environment of the country or region where it is located makes it difficult to ensure data security;
- Responsibilities when one party violates data protection obligations, as well as binding and enforceable dispute resolution clauses;
- Emergency measures in the event of data leakage and other risks, as well as channels for individuals to protect their personal information rights.
When agencies conduct security assessments for data exports, they should take into account the following factors:
- The legitimacy and necessity of the purpose, scope, and method of data export;
- The data security protection policies and regulations of the country or region where the overseas data recipient is located and the impact of the network security environment on data security; whether the data protection level of the overseas recipient meets the laws, administrative regulations and mandatory national standards of China;
- The quantity, scope, type, and sensitivity of exported data, and the risks of leakage, alternation, loss, destruction, transfer, or illegal seizure or use during and after data exportation;
- Whether data security and personal information rights can be fully and effectively protected;
- Whether the contracts between the data processors and the overseas recipients fully stipulate the responsibility and obligation of data security protection;
- Compliance with Chinese laws, administrative regulations, and departmental rules;
- Other matters deemed necessary by cybersecurity agencies.
The draft also lays out the timeline for administrative security review. The agency should decide whether to accept the declaration within seven days. Once accepted, it should complete the review in most cases within 45 days and can be extended up to 60 days in “complicated circumstances” or when additional materials are needed.
A successful security review would be valid for two years. But data processors will have to resubmit for assessment when the purpose, method and scope of exported data is changed, or data processing methods or actual control rights of overseas recipients is changed, or when there are “changes in the legal environment of the country or region where the overseas receiver is located.”
Previously, the CAC issued a draft of security assessment for personal information and important data (link in Chinese) back in 2017, and then in 2019, it issued another draft of security assessment for personal information. Neither draft was finalized.
Compared to the 2017 draft, the new draft adds an extension of the administrative assessment. It also adds some factors to be considered in administrative assessment, such as “whether the contracts between the data processors and the overseas recipients fully stipulate the responsibility and obligation of data security protection.”
In addition, the draft revises the scope of data exports covered by the security assessment, as illustrated in the table below: